Setting up a new AWS environment for evaluation and testing purposes can be done easily and quickly. This is one of the known advantages of AWS, so your developers can start quickly to implement and test new applications. Over time, more and more governance aspects will occur and a multi account strategy will be needed (more in this A&B blog). However, this in turn will increase the complexity of the administration of your application. So do you have to choose between agility for your developers and control for your administrators? The answer is: No! AWS Control Tower can help you with the setup and control of your multi account AWS environment securely.
What is AWS Control Tower?
AWS Control Tower is not a completely new tool. Instead it is an AWS service, which uses other existing AWS services like AWS Landing Zone Solution. A landing zone is an (AWS) environment based on best practices concerning the configuration, where you can build and run your application in a secure multi-account environment. Thus, the landing zone is the starting point for your developers and your administrators in a DevSecOps way.
Working with AWS Control Tower
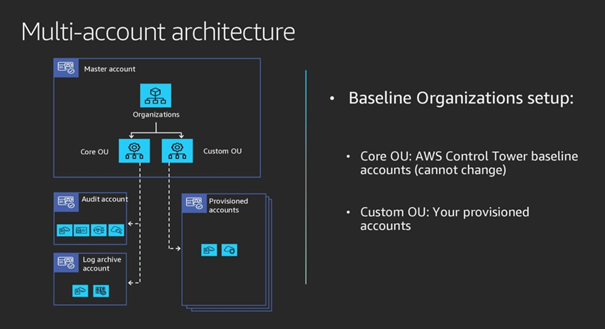
In the first step you setup and configure your AWS environment with a few clicks in AWS Control Tower. This will create some basic accounts based on best practices, for example a logging account and an own account for audit purposes. This results in a number of Core Organizational Units (OU), which should not be changed later on. It also provides the basics for automate compliant account provisioning, which enables your project members to create new accounts later on (Custom Organizational Units) without entering billing information or other standardized information for each new account.
While the Core OUs should not be changed, the Custom OUs are used to create special accounts for different purposes, for example developer accounts or individual business user accounts.
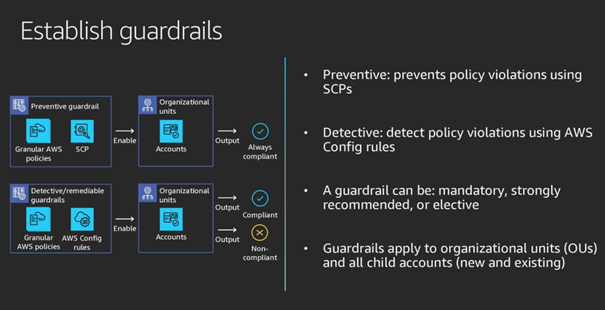
But of course as an administrator you must have the possibility to ensure, that these accounts are compliant with established policies of your organization. You can do this in the second step by defining Service Control Policies (SCPs) and guardrails. By using Service Control Policies you define which AWS service APIs are allowed (allowlist) and which APIs must be blocked (blocklist). The SCPs are assigned to Organizational Units as preventive guardrails. The goal here is preventing policy violations. Detecting policy violations is the goal of detective guardrails, which can be defined using AWS Config Rules.
And finally after creating the accounts and guardrails, AWS Control Tower provides a dashboard with visual summaries of your AWS environment, containing all Organizational Units and accounts together with their status against the defined guardrails.
Who should have a look at AWS Control Tower?
If you are new to AWS, you will normally start with a small use-case. If this is the starting point for your product development, you will quickly reach the point, where you need more than one account, for example when you want to split accounts for billing purposes or you want to separate logging or audit functionalities into special accounts. Although setting up additional accounts can be done manually, this is the right time to have a look at AWS Control Tower: instead of manually copy and paste existing accounts, you can use the best practices provided with AWS Control Tower to design a flexible multi account architecture for your applications.
But even if you already have a running AWS application with manually created accounts and/or you already use AWS Landing Zone Solution you should have a look at AWS Control Tower – which is based on AWS Landing Zone Solution – and check, whether a switch to AWS Control Tower will be the right step now to have a more flexible way for your DevSecOps.
We are happy to assist you with AWS Control Tower. As a newcomer as well as an experienced AWS user, contact us at Alice&Bob.Company!